Continuous compliance is the practice of maintaining ongoing adherence to regulatory requirements, security standards, and internal policies – rather than scrambling to prepare for periodic audits. Instead of treating compliance as a yearly project that consumes weeks of preparation, continuous compliance builds monitoring, evidence collection, and control validation into daily operations.
For organizations managing frameworks like ISO 27001, SOC 2, DORA, NIS2, or PCI DSS, the shift from periodic to continuous compliance monitoring is not optional anymore. Regulators expect real-time oversight, customers demand up-to-date certifications, and the complexity of modern cloud environments makes point-in-time snapshots unreliable.
This guide covers what continuous compliance means in practice, why it matters, how to implement it, and which continuous compliance tools and automation platforms make it achievable without drowning in manual work.
What is Continuous Compliance?
Continuous compliance is a security and governance approach where organizations monitor, test, and validate their compliance posture on an ongoing basis – not just before an audit. The goal is to be audit-ready at any point in time, rather than spending 3-6 months preparing for a single evaluation.
In a traditional compliance model, organizations prepare documentation, gather evidence, and test controls in the weeks or months leading up to an audit. Gaps are discovered late, remediation is rushed, and the entire cycle restarts the following year.
In a continuous compliance model, the cycle never stops. Controls are monitored in real time. Evidence is collected automatically. Gaps trigger immediate alerts rather than appearing as surprises during an audit.
Key Difference
This distinction matters most for frameworks that evaluate operating effectiveness over time. A SOC 2 Type II audit, for example, reviews a minimum 6-month observation window.
If a control failed for two weeks in month three but was fixed before the auditor arrived, the failure is still documented in the report. Continuous compliance monitoring catches that failure in real time so it can be resolved within hours, not weeks.
Why Continuous Compliance Matters
The shift toward continuous compliance is driven by three forces that are only accelerating: regulatory pressure, customer expectations, and the complexity of modern infrastructure.
Regulatory Pressure: Frameworks Now Expect Ongoing Oversight
The newest generation of compliance frameworks explicitly requires continuous processes. DORA (Digital Operational Resilience Act), which became enforceable in January 2025, mandates ongoing ICT risk monitoring, regular resilience testing, and real-time incident reporting for financial institutions across the EU.
NIS2, the EU’s updated network and information security directive, similarly requires continuous risk management and incident notification within 24 hours. These are not annual checkbox exercises – they are operational requirements that assume continuous oversight.
Even established frameworks are moving in this direction. ISO 27001:2022 places greater emphasis on continuous improvement (Clause 10.1) and requires organizations to monitor and measure their ISMS performance on an ongoing basis (Clause 9.1).
Customer Expectations: Compliance Is a Sales Requirement
For B2B SaaS companies, compliance certifications are no longer differentiators – they are table stakes. Enterprise buyers increasingly require SOC 2 Type II reports, ISO 27001 certificates, or DORA compliance documentation before signing contracts.
A certification that is 11 months old raises questions. A continuously maintained compliance posture, backed by real-time dashboards and current evidence, closes deals faster. Companies that can demonstrate continuous security compliance spend less time in procurement review cycles.
Infrastructure Complexity: Point-in-Time Snapshots Are Not Enough
Modern organizations run across multiple cloud providers, SaaS tools, and hybrid environments. Configuration drift happens daily – a developer changes an S3 bucket permission, a contractor’s access is not revoked on time, an SSL certificate expires quietly.
Annual audits cannot catch these issues. Continuous compliance monitoring can. By connecting to cloud infrastructure (AWS, Azure, GCP), identity providers, and DevOps pipelines, continuous compliance tools detect drift the moment it happens.
Core Components of Continuous Compliance
Implementing continuous compliance is not about buying a single tool. It requires building a system of interconnected capabilities across monitoring, automation, documentation, and governance.
1. Continuous Compliance Monitoring
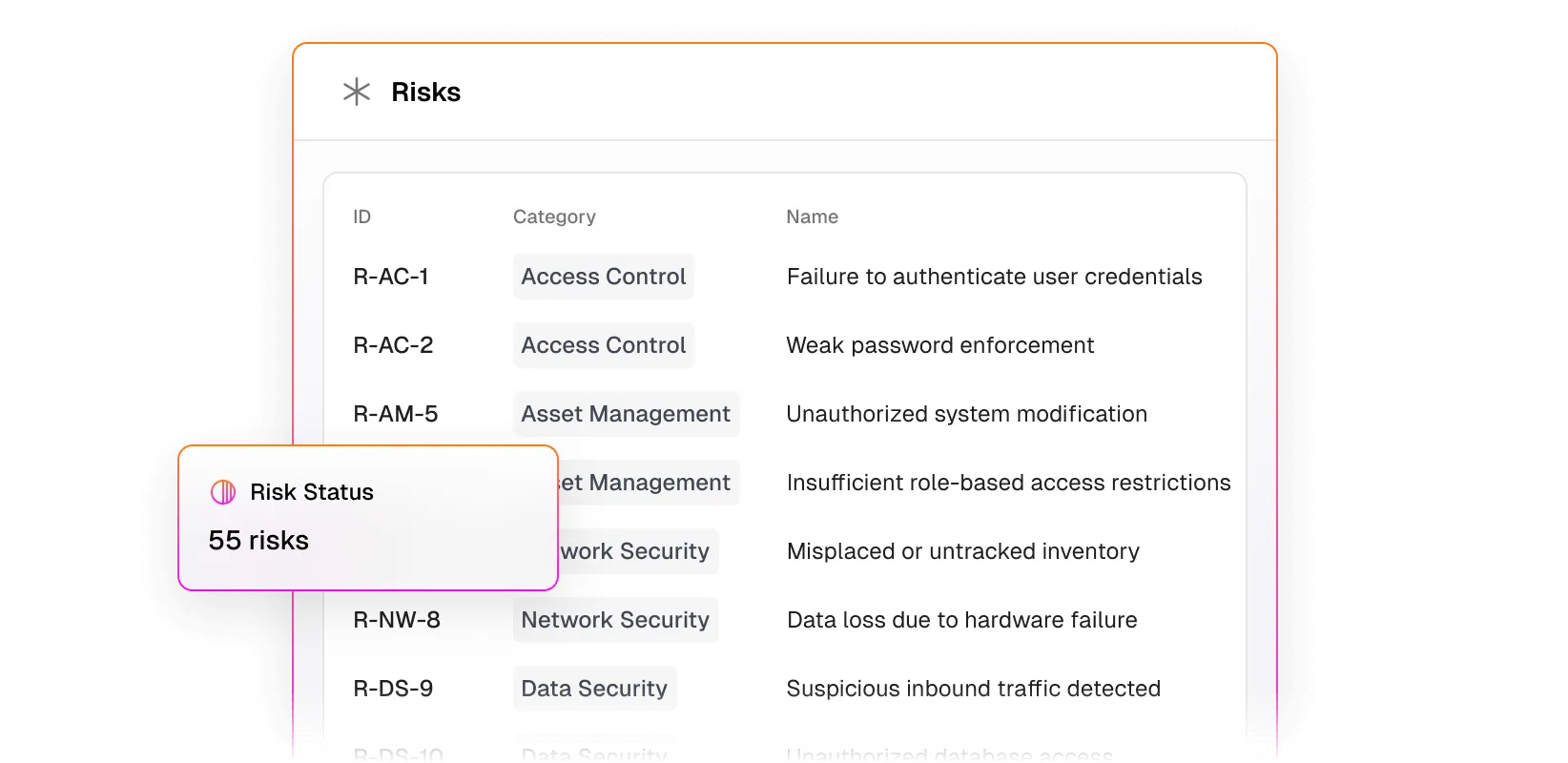
Continuous compliance monitoring is the foundation. This means real-time tracking of control status across your entire environment – security configurations, access permissions, encryption settings, vulnerability scan results, and policy adherence.
Effective compliance monitoring covers three layers:
- Technical controls: These are the automated checks that run against your cloud configurations, network security rules, encryption standards, and endpoint protection policies. They verify that your infrastructure matches your documented security requirements at all times.
- Operational controls: This layer covers the ongoing verification of processes like access reviews, change management workflows, and incident response procedures. It ensures that the processes your team follows in practice match what your policies describe.
- Administrative controls: These track policy acknowledgments, training completion, background checks, and vendor assessments. They confirm that the people side of compliance – awareness, accountability, and third-party governance – stays current.
The goal is not to monitor everything – it is to monitor every control that an auditor would evaluate, and to do so continuously rather than periodically.
2. Automated Evidence Collection
Evidence collection is the most time-consuming part of any compliance audit. In a continuous model, evidence is collected automatically as a byproduct of normal operations.
Compliance automation platforms connect to your existing tools – cloud providers, identity management systems, HR platforms, ticketing systems – and pull evidence in real time. Access review logs, configuration snapshots, training records, and vulnerability scan results are captured automatically and stored in a central evidence repository.
This eliminates the “evidence scramble” that typically consumes 40-60% of audit preparation time.
3. Control Mapping Across Frameworks
Most growing organizations need to comply with multiple frameworks simultaneously. A SaaS company selling to enterprise customers in the EU might need SOC 2, ISO 27001, and DORA compliance at the same time.
Continuous compliance platforms map overlapping controls across frameworks. A single access management control might satisfy requirements in SOC 2 (CC6.1), ISO 27001 (A.9.2), and DORA (Article 9) simultaneously. Implementing it once and mapping it to all three frameworks eliminates duplicated effort.
4. Real-Time Gap Detection and Alerting
When a control drifts out of compliance – whether it is an expired certificate, a misconfigured firewall rule, or an employee who has not completed mandatory training – the system should alert the responsible owner immediately.
This is where continuous compliance testing becomes critical. Rather than discovering gaps during an annual audit, automated tests run continuously and flag issues as they occur. The remediation window shrinks from months to hours.
5. Audit-Ready Reporting
The ultimate output of a continuous compliance program is the ability to generate a complete, auditor-ready report at any time. This report shows the status of every control, with linked evidence, over the relevant observation period.
When an auditor requests evidence for a specific control, the response should take minutes – not days of digging through shared drives and email threads.
How to implement Continuous Compliance: A Step-by-Step Guide
Moving from periodic to continuous compliance does not happen overnight. Here is a practical implementation path that works for organizations of any size.
Step 1: Baseline Your Current Posture
Start by mapping your current compliance status against the frameworks you need to meet. This means conducting a gap analysis – identifying which controls are in place, which are partially implemented, and which are missing entirely.
Document your current state honestly. A gap analysis is only useful if it reflects reality, not what you wish your compliance posture looked like.
Step 2: Assign Control Ownership
Every control needs a named owner. Not a team, not a department – a specific person who is responsible for ensuring the control operates effectively and for providing evidence when needed.
Without clear ownership, controls fall through the cracks. Access reviews do not happen on schedule. Policies are not updated. Training records are not maintained. This is the single most common root cause of audit failures.
Step 3: Automate Evidence Collection
Connect your compliance platform to the systems that generate evidence:
- Cloud infrastructure (AWS, Azure, GCP): Pulls configuration snapshots, security group settings, encryption status, and resource inventories automatically. This is the richest source of technical compliance evidence for most SaaS companies.
- Identity providers (Okta, Azure AD, Google Workspace): Captures access management evidence including user provisioning, deprovisioning, role assignments, and multi-factor authentication enforcement. Critical for access review controls.
- HR systems (BambooHR, Workday, Personio): Tracks onboarding and offboarding workflows, security awareness training completion, background check records, and policy acknowledgments. These feed directly into administrative compliance controls.
- DevOps tools (GitHub, GitLab, Jira): Provides change management and code review evidence. Automated evidence of pull request approvals, branch protection rules, and deployment workflows satisfies change control requirements across SOC 2 and ISO 27001.
- Vulnerability scanners: Feeds vulnerability management and remediation evidence into the compliance platform. Auditors want to see not just that scans were run, but that identified vulnerabilities were triaged and resolved within defined SLAs.
- Endpoint management (Jamf, Intune): Verifies device compliance including encryption status, OS patch levels, and security agent installation. This is especially important for distributed and remote teams where endpoint visibility is harder to maintain manually.
The more integrations you establish, the less manual evidence collection remains. The goal is to automate 80% or more of evidence gathering.
Step 4: Set Up Continuous Monitoring and Alerts
Configure your continuous compliance monitoring to check control status on a defined frequency – ideally daily or real-time for critical controls, weekly for lower-risk items.
Set up alerts that route to the control owner when a check fails. The alert should include what failed, why it matters, and how to fix it. Without actionable alerts, monitoring generates noise instead of value.
Step 5: Run Internal Audits Quarterly
Even with continuous monitoring, periodic internal audits remain valuable. They catch process-level issues that automated checks cannot – like whether risk assessments are genuinely thorough, or whether incident response procedures actually work under pressure.
Schedule internal audits quarterly. Use the findings to refine your monitoring rules, update your control catalog, and improve your automation coverage. For a detailed guide on preparing for these audits, see our compliance audit preparation guide.
Step 6: Review, Improve, Repeat
Continuous compliance is a continuous improvement process. Review your monitoring coverage monthly. Assess new regulatory requirements as they emerge. Expand automation to cover newly identified gaps. Update your control catalog as your infrastructure evolves.
ISO 27001 Clause 10.1 explicitly requires this cycle: act on non-conformities, analyze root causes, determine if similar issues exist elsewhere, and implement corrective actions.
Continuous Compliance Tools: What to Look For
The market for continuous compliance tools has grown rapidly. The right platform should cover monitoring, evidence collection, control mapping, and reporting in a single system. Here is what matters when evaluating options.
| Capability | Why It Matters | What to Look For |
|---|---|---|
| Framework coverage | You will likely need multiple frameworks | SOC 2, ISO 27001, DORA, NIS2, PCI DSS, HIPAA at minimum |
| Integrations | More integrations = less manual evidence work | Native connectors for your cloud, identity, HR, and DevOps stack |
| Control mapping | Reduces duplication across frameworks | Automated cross-framework mapping with overlap visualization |
| Real-time monitoring | Catches drift before auditors do | Continuous checks, not just periodic scans |
| Alert routing | Issues must reach the right person | Integration with Slack, email, or ticketing systems |
| Audit-ready exports | Saves weeks during audit season | One-click report generation with linked evidence |
| Expert support | Software alone cannot replace human judgment | Access to compliance experts or vCISO services |
Leading Continuous Compliance Platforms
Several platforms compete in this space, each with different strengths:
- Copla: EU-based platform covering ISO 27001, SOC 2, NIS2, DORA, and PCI DSS with real CISO support and audit representation included in every plan. Starting at EUR 2,999/year for a single framework with a 20% discount on additional frameworks. Strong differentiator for financial institutions: a dedicated DORA Registry tool built specifically for ICT third-party risk reporting.
- Drata: One of the broadest integration libraries in the market with 85+ native connectors, making it a popular choice for US-based SaaS companies pursuing SOC 2 and ISO 27001. Its continuous monitoring engine automates evidence collection from connected systems and provides real-time control status dashboards.
- Vanta: A trust management platform with strong SOC 2 and ISO 27001 coverage that also offers a customer-facing trust center for sharing your compliance posture with prospects during the sales process. Particularly well-suited for fast-growing startups that need to demonstrate compliance quickly.
- Secureframe: Supports SOC 2, ISO 27001, HIPAA, PCI DSS, and several additional frameworks. Stands out with automated employee onboarding workflows for compliance training and policy acknowledgment, reducing the administrative burden on security teams.
- Sprinto: Takes an automation-first approach with strong SOC 2 and ISO 27001 coverage. Known for its fast time-to-compliance and developer-friendly workflows that integrate directly with engineering tools and CI/CD pipelines.
- Hyperproof: A compliance operations platform designed for organizations managing multiple frameworks simultaneously. Its strength lies in compliance management workflows and cross-framework control mapping that help teams reduce duplication across SOC 2, ISO 27001, HIPAA, and other standards.
For a full comparison of these tools and others, explore our compliance software category on Tekpon.
Continuous Compliance Automation: Manual vs. Automated
Continuous compliance automation replaces manual processes with technology-driven workflows. The difference in effort, cost, and reliability is significant.
| Process | Manual Approach | With Continuous Compliance Automation |
|---|---|---|
| Evidence collection | Weeks of chasing screenshots, exports, and email confirmations from multiple teams | Automated via integrations - evidence pulled continuously from connected systems |
| Control monitoring | Quarterly spot checks at best. Failures discovered during audit. | Real-time checks with instant alerts when a control drifts |
| Access reviews | Manual spreadsheet comparison every 90 days | Automated access review triggers with approval workflows |
| Policy management | Policies stored in shared drives, version control via email | Centralized policy hub with tracked acknowledgments and automated reminders |
| Vendor assessments | Annual questionnaires sent via email, tracked in spreadsheets | Vendor risk profiles with continuous monitoring of third-party posture |
| Audit preparation | 3-6 months of dedicated effort before each audit | Always audit-ready - generate reports in minutes |
The ROI calculation is straightforward. Organizations that implement continuous compliance automation typically reduce audit preparation time by 60-80% and cut the risk of non-conformities significantly.
For growing companies managing multiple frameworks, the cost of compliance without automation quickly exceeds $100,000 annually in staff time and consultant fees alone.
How Copla Powers Continuous Compliance
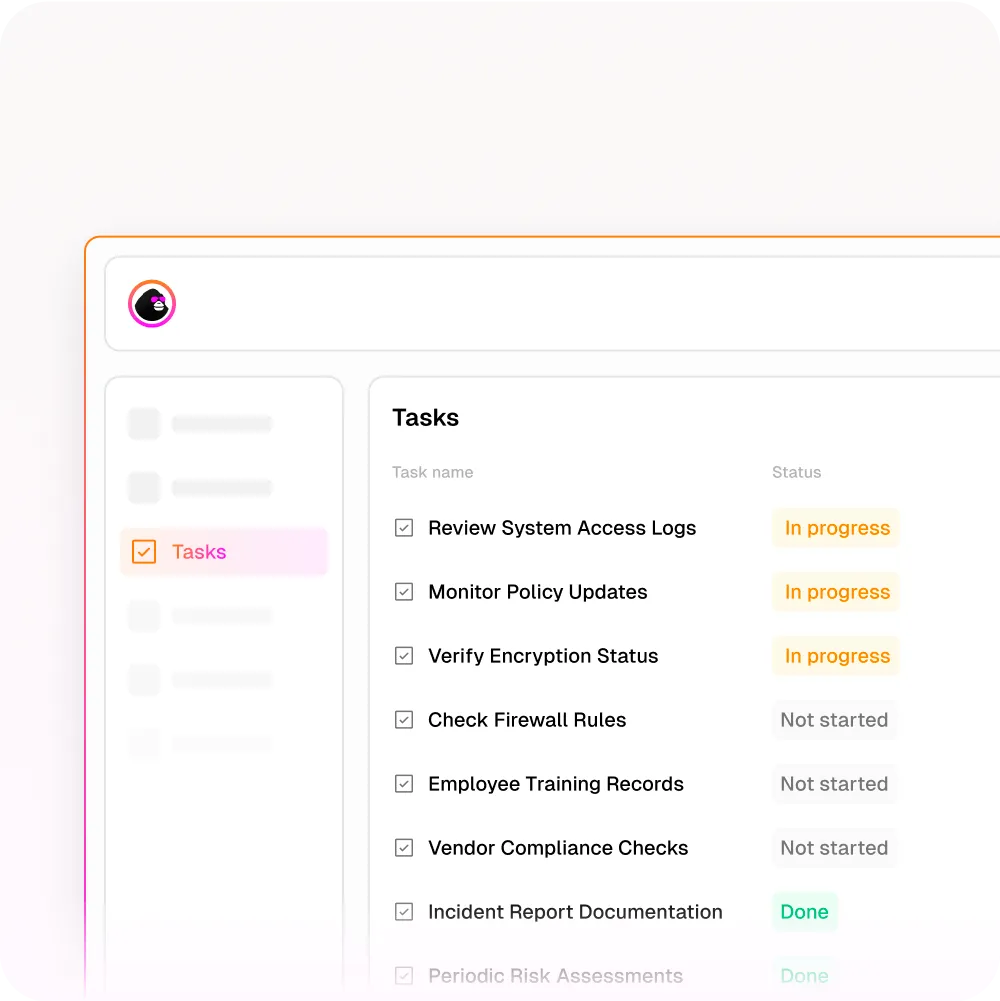
Continuous compliance depends on automation and integrated technology. Manual processes slow teams down and make audit readiness a quarterly sprint. Copla changes that by turning compliance into an ongoing, automated activity.
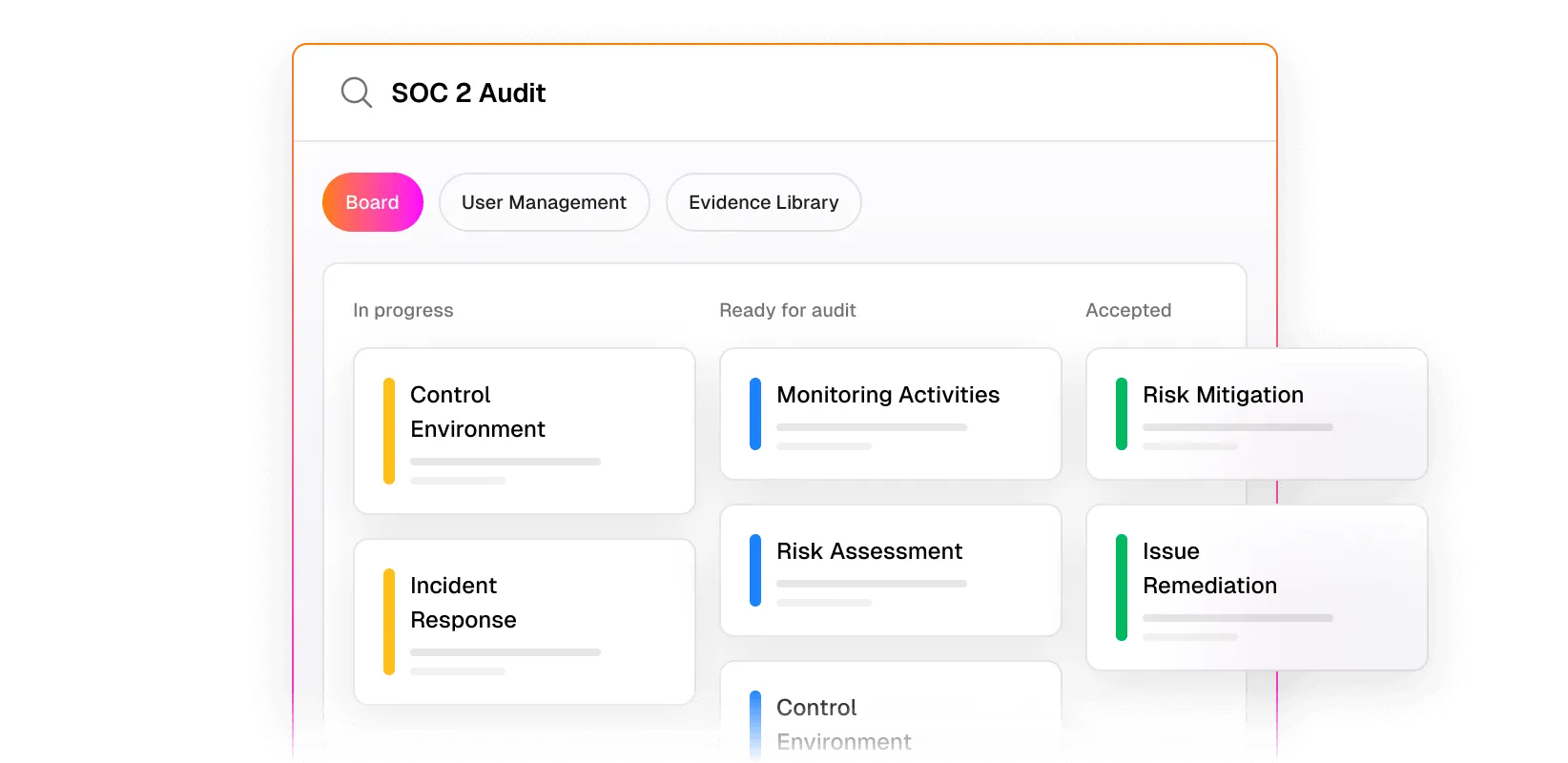
Copla acts as a central compliance hub where workflows, controls, evidence, and risk data live together. It continuously collects audit-ready evidence from cloud environments, collaboration tools, identity systems, and security scans.
This automated evidence-collection engine means documentation is always up to date without manual pulling of logs, screenshots, or spreadsheets.
Copla stores evidence in a structured repository that auditors can access directly, cutting hours of prep work.
Real-time monitoring is built into Copla. The platform tracks control status and flags deviations as they happen. If a configuration drifts from policy or a periodic access review is overdue, Copla sends alerts and assigns tasks so teams can fix issues early, not weeks after they occur.
Instead of separate point tools, Copla bundles continuous compliance capabilities into one platform. It maps controls automatically to frameworks such as SOC 2, ISO 27001, DORA, GDPR, and NIS2, saving time on cross-framework correlation and evidence reuse.
Prebuilt, customizable workflows guide teams through required actions, and Slack or Teams integrations bring compliance nudges directly into daily workstreams.
Copla also pairs intelligent automation with expert guidance. Fractional CISOs help shape compliance strategy, prioritize risks, and refine controls. This hybrid model ensures that automation does not just run tasks; it reinforces best practices and reduces up to 80% of manual compliance effort, freeing teams to focus on core business goals.
Continuous Cloud Compliance
For organizations running on AWS, Azure, or GCP, continuous cloud compliance deserves special attention. Cloud environments change constantly – new instances spin up, configurations are modified, permissions evolve – and each change can introduce compliance gaps.
Continuous cloud compliance means applying compliance monitoring directly to your cloud infrastructure through native APIs. Key areas to monitor include:
- Identity and access management: Continuous checks on who has access to what, whether permissions follow least-privilege principles, and whether inactive accounts have been deprovisioned. IAM misconfigurations are the most common cloud compliance finding.
- Data encryption: Automated verification that data is encrypted at rest and in transit across all services. A single unencrypted S3 bucket or database instance can trigger a non-conformity in SOC 2, ISO 27001, or PCI DSS audits.
- Network security: Ongoing monitoring of security groups, firewalls, and VPC configurations to confirm they align with your documented policies. Network rule changes should trigger compliance re-evaluation automatically.
- Logging and monitoring: Verification that audit trails are enabled for all critical services and that logs are being retained for the required duration. Many frameworks require specific log retention periods, and disabled logging is a common drift issue.
- Configuration management: Continuous validation that cloud resources are configured according to CIS benchmarks or your internal standards. Configuration drift is inevitable in dynamic cloud environments, and catching it early prevents both compliance gaps and security exposures.
AWS Config Rules, Azure Policy, and GCP Security Command Center provide native continuous compliance testing capabilities. However, these tools are cloud-specific – if you run a multi-cloud or hybrid environment, you need a platform that aggregates compliance data across all providers into a single view.
Continuous Compliance Best Practices
Based on how organizations successfully operate continuous compliance programs, these practices consistently make the difference between a system that works and one that becomes shelfware.
- Start with one framework, then expand: Get one framework running continuously before adding others. The cross-mapping benefits only work when the first framework is solid. Trying to implement SOC 2, ISO 27001, and DORA simultaneously leads to shallow coverage across all three.
- Automate the boring stuff first: Evidence collection, access reviews, and training tracking are high-volume, low-judgment tasks that consume the most staff time. Automate them first for the biggest immediate time savings, then gradually extend automation to more complex controls.
- Make compliance monitoring visible: Dashboard visibility for leadership and control owners keeps the program alive. When compliance data is hidden in a tool that only one person checks, the program slowly dies. Real-time dashboards shared with executives maintain accountability.
- Integrate with existing workflows: Compliance alerts should arrive in Slack, Jira, or whatever tools your team already uses on a daily basis. Creating a separate compliance workflow that sits outside your team’s normal tooling guarantees it will be ignored.
- Assign real ownership, not committees: Every control needs one named person who is accountable for its status. Committees diffuse responsibility and slow remediation. When everyone is responsible, nobody is responsible.
- Run tabletop exercises: Test your incident response, business continuity, and disaster recovery plans through live simulations at least twice a year. Documented procedures that have never been tested under pressure are one of the most common audit findings across SOC 2 and ISO 27001.
- Track metrics that matter: Measure mean time to remediation, percentage of controls passing continuously, evidence freshness, and alert response time. These metrics give you a quantitative view of compliance health and make trends visible before they become problems.
- Budget for expert support: Compliance automation tools handle the mechanics, but regulatory interpretation still requires human expertise. Build CISO access into your budget – whether fractional, full-time, or platform-included like Copla’s bundled CISO services.
Continuous Compliance FAQ
Unlike traditional periodic compliance where organizations prepare intensively before each audit, continuous compliance ensures the organization is audit-ready at all times. It relies on automation to track control effectiveness, collect evidence, and alert teams when a control drifts out of compliance.
When a check fails, the system alerts the responsible control owner so the issue can be remediated before it becomes an audit finding. Leading compliance software platforms provide this capability through native integrations with cloud infrastructure, identity providers, and business tools.
Controls are monitored continuously, evidence is collected automatically, and gaps are flagged in real time. The result is lower preparation costs, fewer audit findings, and the ability to generate audit-ready reports at any time rather than only during audit season.
The cost should be weighed against the alternative: manual compliance preparation typically costs $50,000-$150,000 annually in staff time and consultant fees for a mid-size company. For a detailed breakdown, see our guide on the real cost of compliance for SaaS companies.
The most important principle is that compliance must be integrated into daily workflows – not treated as a separate project that only activates before audits. For a step-by-step implementation guide, see the section above.
When you maintain continuous compliance, the audit becomes a verification exercise rather than a discovery exercise. Evidence is already collected, controls are already documented, and gaps have already been remediated.
Native tools like AWS Config Rules, Azure Policy, and GCP Security Command Center provide some of this capability, but multi-cloud environments require a unified platform that aggregates compliance data from all providers. For organizations running on cloud security software, continuous monitoring is essential because cloud configurations change constantly.